The Long View: Using Regret Minimization to Build a Remarkable Business
·7 mins
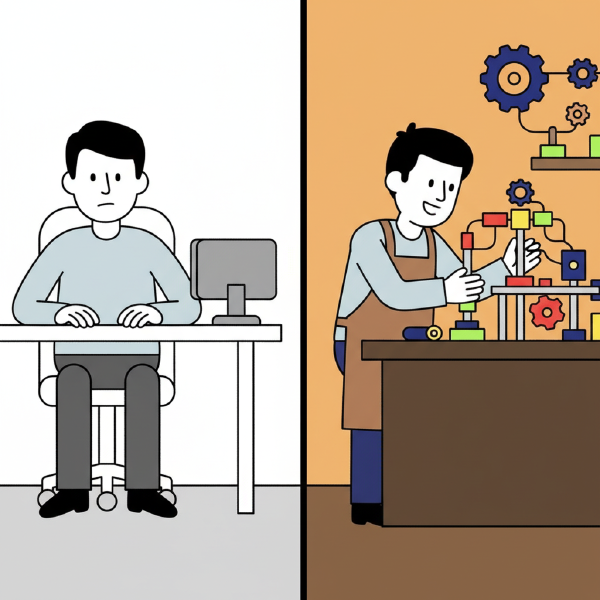
This article explores the Regret Minimization Framework as a tool for entrepreneurs to prioritize long-term impact and personal fulfillment over temporary security and short-term comfort.